The EOD Disruptor is a 4th generation 30 mm Midi Disrupter featuring, variable projectile mass and recoilless operation. It can be configured as:



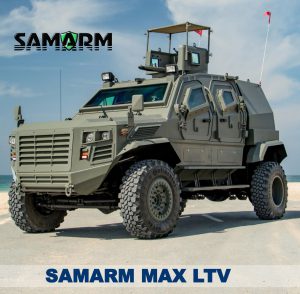
samarmMaxExp2











Toyota Land Cruiser 200 VIP version Armored in B6 class according to the CEN standards
This is prepared with the best quality materials and fabricated by skilled technicians.
This protection is to European B6 level and is certified to defeat the following ammunition:
7.62 x 51 RG L2A2 at 843 m/s 7.62 x 39 PS 1943 ball at 709 m/s 5.56 x 45 RG L2A2 at 931 m/s FNB SS109 at 942 m/s and lesser threats
Armouring: Sides – plates thickness 6 mm ARMOX T 500/5 mm ARMOX T 600 Floor – plates thickness 4 mm ARMOX T 500 – protection against two DM51 hand grenades Roof – plates thickness 4 mm ARMOX T 500 Glass – thickness 38 mm

Multi-Layer-Application tactical system that interrogates and identifies any GSM/UMTS mobile handset from the air.
Product versions:
All versions available in various modes of operation:
Operational Applications:
Operational benefits:

Can be connected to:

Our products for Law Enforcement

Simple stand-alone single-line „personal recorder”. Can be connected to:
Market: Law Enforcement
Requirements/applications:

Multi-channel call recorder. Can be connected to:
All recordings are stored on internal HDD or NAS. Max. 32 channels/PC

Multi-channel call recorder. Can be connected to:
Standard analogue telephone lines
Radiotelephones
Digital PBX telephone lines
ISDN (E1/30B+D or U/S0/2B+D) lines
VoIP
All recordings are stored on internal HDD or NAS. Max. 512 channels/PC.



Audio recording may be used in the court as evidence, but sometime the recording may have loud background noise that cause the recording to be useless.
At Mentari Setia, we have specialist for audio enhancement. His job is to remove static background noise and improve overall audio clarity and intelligibility.
The purpose of the mobile jammer is to ensure protection against radio-controlled bombs. It can protect single or group moving objects, groups of people, cars and/or other small area targets the security of the working personnel is guaranteed according to the standards BDS17137-90, European Union standard SAR and the NATO standard STANAG 2345
The purpose of portable jammer is to ensure protection against radio-controlled bomb. It can protect single or group moving objects, groups of people, cars or any other small object
List of jammed devices
The purpose of Manpack Jammer is to ensure protection against radio-controlled bomb. It can protect single or group moving objects, groups of people, cars or any other small object


<p>Passwords can be forgotten through lack of use or from auto generated changes. Or they can simply cease to work for no apparent reason. This may prohibit the user from using the computer, but in other cases it may require thousands of password protected files to be deleted if the overriding password cannot be determined. Where special encryption has also been involved, the task becomes even more difficult.
we are experts at cracking password protected files and systems. Using our extensive library of software, techniques and cracking resources we may be a critical resource when crucial files are encrypted. We can also perform security analysis and provide un-crackable encryption software and state of the art firewalls and network security software for those who value privacy and want to be sure their data is secure.</p>
Audio Forensics / Voice Investigation / Voice Forensics is the field of forensic science relating to the acquisition, analysis, and evaluation of sound recordings that may ultimately be presented as admissible evidence in a court of law or some other official venue
The primary aspects of audio forensics are:
As an Audio Forensic Expert and Expert Witness, Mentari Setia has analyzed hundreds of audio recordings for authentication, clarification and voice identification in both analogue and digital formats.
The following list describes types of forensic services Mentari Setia offer as an expert witness:
Disk cloning is the process of copying the contents of one computer hard disk to another disk or to an “image” file. This may be done straight from one disk to another, but more often, the contents of the first disk are written to an image file as an intermediate step, then the second disk is loaded with the contents of the image. Typically, this is done for archiving purposes, to restore lost or damaged data, or to move wanted data into a new disk, though other reasons also exist.
Unlike standard copying functions, disk cloning involves copying hidden and in-use files, and thus presents special challenges, as those types of files are typically not available for copying. Additional complications arise when the process is used for networked computers, as the network must be able to distinguish between different computers.
Anti Forensics</b> is simply a breaking tool and a growing methods and collection of tools used to prevent or against the application of science to those criminal and civil laws that are enforced by criminal justice system
Goals of Anti-Forensics: